AI agents found vulns in this popular Linux and Unix print server

Foto: The Register
Two critical vulnerabilities in the most popular printing system for Linux and Unix systems, CUPS, have been discovered by AI agents operating under the supervision of a SpaceX security engineer. The flaws, designated as CVE-2026-34980 and CVE-2026-34990, allow an unauthenticated attacker to achieve remote code execution (RCE) and overwrite system files with root privileges. The issue affects CUPS version 2.4.16, which is standard in most Linux distributions and Apple operating systems. The attack exploits the default CUPS policy that accepts anonymous print jobs on shared networks. By manipulating PPD control records and exploiting newline parsing errors, hackers can inject malicious code directly into the print queue. While this scenario primarily concerns corporate environments with shared print servers, the scale of the threat is immense due to the ubiquity of this software. For users and administrators globally, this necessitates immediate verification of network configurations and restricting access to CUPS ports. Despite the lack of an official version 2.4.17, patches (commits) have already appeared in open-source repositories and should be implemented before LLM-based automated tools begin mass-generating ready-to-use exploits based on published analyses. This serves as further evidence that AI is becoming a key tool for bug hunters, drastically accelerating the process of finding vulnerabilities in critical infrastructure.
In the world of cybersecurity, printing systems have long been considered a rewarding target for attacks — they are ubiquitous, rarely updated, and often run with high privileges. However, the latest discovery regarding CUPS (Common Unix Printing System) brings this problem to a whole new level. It is not just about the scale of the threat itself, but the way it was identified: using specialized AI agents that proved they can find vulnerabilities where traditional audits failed.
Asim Viladi Oglu Manizada, a security engineer at SpaceX, along with his team of digital "bug hunters," revealed two critical vulnerabilities in CUPS 2.4.16. These flaws, designated as CVE-2026-34980 and CVE-2026-34990, can be linked into an exploit chain, allowing an unauthenticated attacker to achieve remote code execution (RCE) and overwrite system files with root privileges. This discovery sheds new light on the security of Linux, Unix, and macOS systems, for which CUPS is the standard print handling solution.
The mechanism of a double strike on CUPS architecture
The first piece of the puzzle, CVE-2026-34980, hits the default server policy that accepts anonymous print job requests. The problem arises when a PostScript print queue is shared on the network. While such a configuration is rare in home environments, it is an operational standard in corporate infrastructures. This vulnerability stems from an error in how CUPS handles newline characters in option strings — the system precedes them with a backslash, which is later removed during parsing. An attacker can embed malicious code at this point that "survives" the data sanitization process.
Read also
Exploiting the fact that CUPS treats control records starting with "PPD:" as trusted, a hacker can modify the queue configuration and inject a malicious entry into the printer description file. Consequently, when a second, raw print job is sent, the server is manipulated into executing any binary system file — for example, the Vim text editor — with the privileges of the lp account. This is a classic example of a logic flaw, where correct functionality is used against the system itself.
The second link, CVE-2026-34990, is an authorization error that affects even default CUPS configurations. It allows a local, unprivileged user to trick the scheduler daemon (cupsd) into authenticating to an attacker-controlled IPP service on localhost using a reusable Authorization: Local token. When both vulnerabilities are combined, a remote attacker without any passwords can not only execute code but gain full write access to files as root, which in practice means complete control over the machine.
- CVE-2026-34980: Remote Code Execution (RCE) through PostScript queue manipulation.
- CVE-2026-34990: Privilege escalation to root through system file overwriting.
- Vulnerable version: CUPS 2.4.16 and older, unpatched releases.
- Requirements: Shared print queue for RCE; local access for privilege escalation.
AI agents as a new force in bug hunting
The most intriguing aspect of this case is the role of artificial intelligence. Manizada admitted that AI agents are becoming extremely effective at narrowing the search field. Instead of asking a model to find a ready-made exploit with a single command, researchers divide tasks into smaller stages: searching for any RCE and finding a primitive that allows root access. This approach allows agents to work more precisely and save computing resources.
Michael Sweet, the creator and maintainer of the CUPS project, confirmed the seriousness of the situation, explaining that an error in handling page-border values allows a newline to be smuggled through escaping mechanisms. Although an official, patched binary version did not yet exist at the time of disclosure, public commits with fixes appeared in open-source repositories. Experts warn that since Proof of Concept (PoC) descriptions are already available, and modern LLM models can instantly turn technical analyses into working attack code, the risk of mass exploitation is very high.
This situation shows the growing disparity between the pace at which AI can find vulnerabilities and the ability of human open-source project maintainers to fix them. AI agents do not need sleep or coffee breaks, and their ability to analyze complex dependencies in C or C++ code is becoming a powerful tool in the hands of both researchers and potential cybercriminals. The industry must prepare for a reality where "security through obscurity" — as in the case of old printing protocols — ceases to exist.
"You don't have to discover the whole chain with one prompt. Tasking agents to find specific primitives allows you to drastically narrow the search space and makes the process incredibly efficient," notes Asim Manizada.
It can be assumed with high probability that this is only the beginning of a wave of AI-generated discoveries in mature infrastructure projects. The effectiveness of agents in detecting bugs in CUPS suggests that other critical components of Unix systems, which have not been subjected to rigorous audits for years, may hide similar surprises. In the era of automated bug hunting, the only effective defense strategy becomes equally fast, AI-assisted code verification on the developers' side.
More from Industry
Broadcom agrees to expanded chip deals with Google, Anthropic
OpenAI asks California, Delaware to investigate Musk's 'anti-competitive behavior' ahead of April trial
Hope for a U.S.-Iran deal, Apple's anniversary, OpenAI's podcast deal and more in Morning Squawk
AI data center boom ‘stress tests’ insurers as private capital floods in
Related Articles

Researchers didn’t want to glamorize cybercrims. So they roasted them
Apr 5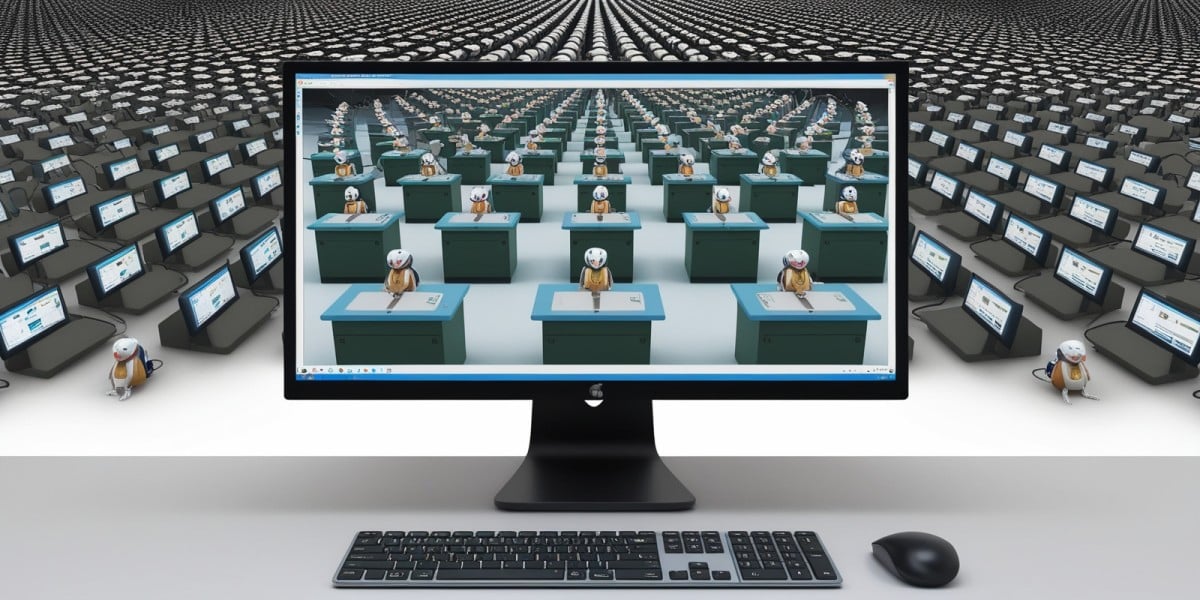
AI agents promise to 'run the business,' but who is liable if things go wrong?
Apr 5
Netflix, Meta, and IBM speakers: AI will make anyone a 10x programmer, but with 10x the cleanup
Apr 4

