Researchers didn’t want to glamorize cybercrims. So they roasted them

Foto: The Register
Instead of awe-inspiring names like Wizard Spider or Velvet Tempest, cybercriminals should be referred to as "Scrawny Intruders" or "Evil Ferrets." During the RSA conference, John Fokker, Vice President of Threat Intelligence at Trellix, announced an end to the mythologizing of hackers as omnipotent entities. The security industry is shifting toward a psychological offensive, launching the "Dark Web Roast" series, where researchers replace dry technical reports with memes and sharp irony to mock the incompetence and greed of digital burglars. In its latest publications, Trellix highlights instances such as ransomware gangs mass-producing fake evidence of attacks to artificially inflate their statistics, or the developer of an exploit for CVE-2026-20045 who became a laughingstock on forums after attempting to sell a publicly known vulnerability for $70,000. This shift in narrative has real-world significance for users and organizations: stripping criminals of their aura of invincibility helps focus on the mundane human errors that are the source of most incidents. It also serves as a signal to law enforcement agencies which—following the example of the British NCA during the dismantling of the LockBit group—are increasingly using trolling as an effective tool to deconstruct criminal structures. Ridiculing hackers strikes at their most valuable currency: their reputation in the underground, which directly hinders their recruitment efforts and ability to build business credibility.
For years, the cybersecurity industry has built an aura of almost mythical elusiveness around hacking groups. Data protection companies gave them menacing names like Wizard Spider or Velvet Tempest, unintentionally creating an image of digital supervillains. However, a new wave of experts, supported by government agencies, is saying "enough." Instead of celebrating their supposed genius, researchers have decided to publicly mock them, exposing the amateurism and greed hidden behind the mask of anonymity.
The end of mythical hacker superpowers
The trend of demystifying cybercriminals is gaining momentum, and its faces include figures like John Fokker, Vice President of threat intelligence at Trellix. During an interview at the RSA Conference, Fokker expressed deep frustration with the way the industry portrays attackers. According to him, treating them as invincible entities does not help organizations in real defense, but only builds unnecessary fear. "These are just individuals who use computers, want to steal your data, and make money. They are not mythical. They don't have superpowers," the expert emphasizes.
Fokker's voice resonates with appeals coming from the top, including from the former head of CISA, Jen Easterly. She advocates for abandoning flashy pseudonyms in favor of names that strip criminals of their gravity. Instead of "Menacing Dragon," the industry should start using terms like "Scrawny Nuisance" or "Evil Ferret". This is a paradigm shift – a transition from fascination to contempt, which has a real impact on the effectiveness of operational activities.
Read also
Dark Web Roast: analysis with a wink
The Trellix team went a step further, implementing a strategy they describe as "psychological operations" (psyops). They launched the Dark Web Roast – a regular series of publications where, instead of dry technical reports, readers find memes, mockery, and ruthless pointing out of hacker mistakes. Although the authors state that the described incidents are harmful crimes, they do not deny themselves the pleasure of mocking absurd situations from the underground.
In one of the recent editions, researchers examined a ransomware gang that prepared its extortion campaigns with the same boring systematicity as social media post schedules. Analysts noticed that with such a massive scale of posts, most "victims" were likely fictional sites created by the hackers themselves to artificially inflate success statistics. Nothing undermines a criminal group's credibility like proof that they have to lie for anyone to take them seriously.
A festival of amateurism and exploit inflation
Source materials provide examples that sound more like comedy-of-errors scripts than technological thrillers. Researchers cite the story of an exploit developer using the pseudonym cortana9000. He discovered an RCE vulnerability in Cisco devices (designated as CVE-2026-20045), which was already being actively exploited by state-sponsored groups. Instead of maintaining professional discretion, the hacker began asking on a forum about the value of the find, pricing it at $70,000.
- KlopInko, another forum user, quickly dampened his enthusiasm, noting that since the vulnerability was already known, it automatically became a "1-day exploit."
- The value of the find began to drop drastically the moment cortana9000 mentioned it.
- Another criminal, patagon, tried to sell full domain administrator access to a Russian power grid for an amount lower than the price of a used car.
Such examples show that the hacking underground lacks not only ethics but often basic market knowledge. Publicly pointing out these mistakes by companies like Trellix serves education, but above all, it hits the ego of criminals who build their authority on alleged infallibility.
Trolling as a law enforcement tool
The new approach to fighting cybercrime has also been adopted by law enforcement. A breakthrough was the operation to seize the infrastructure of the LockBit group, coordinated by the British National Crime Agency (NCA). Instead of simply shutting down the servers, the police took over the hackers' website and began trolling them, using their own countdown timers for data leaks to ultimately reveal the identity of the leader known as LockBitSupp.
Simply removing servers often resembles a game of "whack-a-mole" – hackers just move elsewhere. However, public humiliation and sowing disinformation within hacking structures have much more lasting effects. As John Fokker notes, such actions crumble the foundation of any business: trust. In a world where ransomware groups collaborate with access brokers and external developers, a shadow of suspicion regarding police cooperation or internal fraud can lead to the collapse of the entire ecosystem.
Treachery among thieves
An example of effective discord-sowing was Operation Endgame and actions targeting the Rhadamanthys software in November 2025. The Dutch police, working with Europol and Trellix, discovered that the administrator of this malware was stealing from his own "clients." He intercepted the most valuable cryptographic keys and data for himself, passing on only less valuable scraps of information to buyers.
"We said it straight out: you're stupid if you work with him because he's getting rich off you, and we're laughing at him," Fokker reports.
While hard statistical data on the impact of "roasting" on the decline in the number of attacks is difficult to obtain, the psychological effect is undeniable. A mocked hacker loses business partners, and their brand in the darknet becomes toxic. In an industry that has fed on fear for years, changing the narrative to a mocking one may prove to be one of the most effective defensive methods. Cybercriminals are not digital gods – they are often greedy amateurs who fear only one thing: that someone will finally say out loud how incompetent they really are.
More from Industry
Broadcom agrees to expanded chip deals with Google, Anthropic
OpenAI asks California, Delaware to investigate Musk's 'anti-competitive behavior' ahead of April trial
Hope for a U.S.-Iran deal, Apple's anniversary, OpenAI's podcast deal and more in Morning Squawk
AI data center boom ‘stress tests’ insurers as private capital floods in
Related Articles

The Ridiculously Nerdy Intel Bet That Could Rake in Billions
Apr 6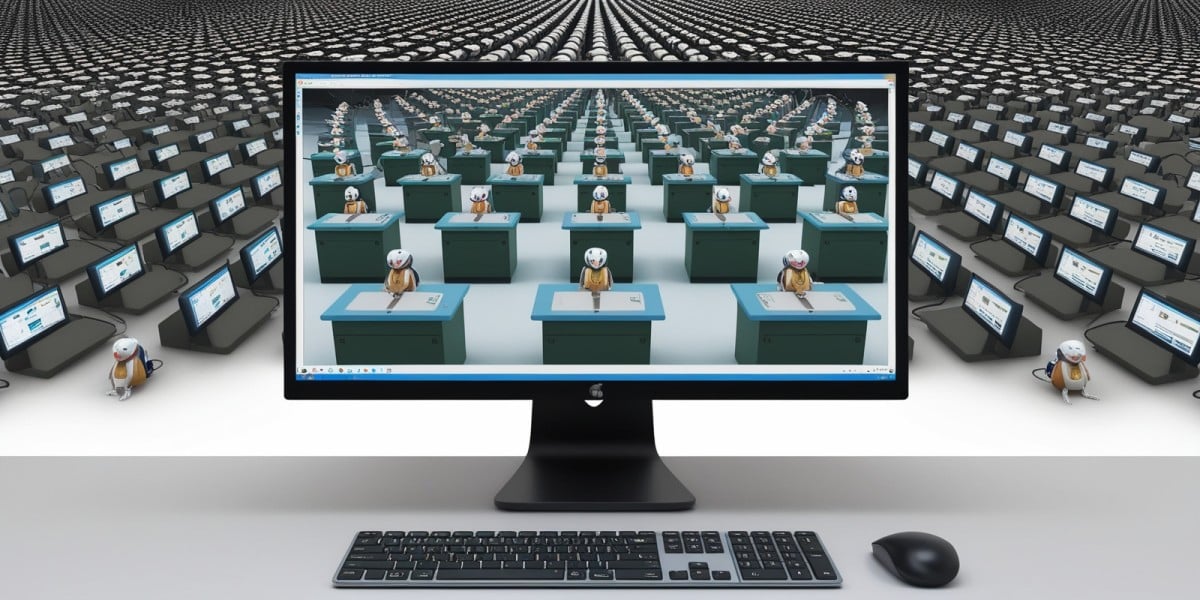
AI agents promise to 'run the business,' but who is liable if things go wrong?
Apr 5
Netflix, Meta, and IBM speakers: AI will make anyone a 10x programmer, but with 10x the cleanup
Apr 4

