‘CanisterWorm’ Springs Wiper Attack Targeting Iran

Foto: Krebs on Security
More than a simple act of cybercrime – the TeamPCP group has officially joined the geopolitical conflict by infecting systems in Iran with the destructive CanisterWorm. The malware is designed to automatically identify targets based on time zone and the default Farsi language, and then irreversibly delete data from infected machines. The attack, which intensified last weekend, represents an evolution in the activities of a group previously known primarily for data theft and financial extortion on Telegram. CanisterWorm spreads in a self-replicating manner, exploiting critical vulnerabilities in cloud infrastructure, including bugs in Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability. For global users of creative technologies and IT administrators, this is a clear signal that poorly secured cloud environments can become tools in hybrid warfare, even if a given organization is not the direct target of the attack. Effective protection now requires not only patching known holes but, above all, rigorous management of permissions and authentication credentials, which are the primary loot for attackers during lateral movement within a network. This incident proves that the line between pure cybercrime and the ideological destruction of digital assets is ultimately blurring.
In the world of cybersecurity, the line between common financial crime and political operations is becoming increasingly blurred. The latest incident involving the CanisterWorm is a stark example of this evolution, where a group previously motivated by profit has decided to carry out a destructive wiper attack. The targets are systems operating in the Iranian time zone and those where the default language is Farsi. This is not a simple data theft – it is digital sabotage aimed at a specific geographic region.
The attack, which intensified over the past weekend, is the work of a relatively new formation known as TeamPCP. This group, operating primarily on the Telegram platform, had until now focused on classic ransomware extortion and data exfiltration. However, the introduction of a destructive mechanism (wiper) as part of a campaign targeting Iran suggests that cybercriminals are attempting to influence the ongoing conflict or use it as a smokescreen for their activities. The scale of the infection is amplified by the fact that CanisterWorm has self-replicating capabilities, making it an exceptionally dangerous tool in the hands of an aggressor.
Automation of destruction through cloud vulnerabilities
The foundation of CanisterWorm's success is the exploitation of poorly secured cloud services, which currently form the backbone of modern IT infrastructure. The worm does not look for specific victims through targeted phishing but scans the network for exposed Docker APIs and Kubernetes clusters. These powerful container orchestration tools, if misconfigured, become an open gate for malware, allowing it to rapidly infiltrate entire corporate environments.
Read also
In addition to container platforms, TeamPCP targets Redis servers and exploits a vulnerability known as React2Shell. After gaining initial access, the worm does not stop at a single node. It is designed to move laterally (lateral movement) within the victim's network. The main goal at this stage is to intercept authentication credentials, allowing the group to take full control over company resources and set the stage for the final blow: deleting all available data.
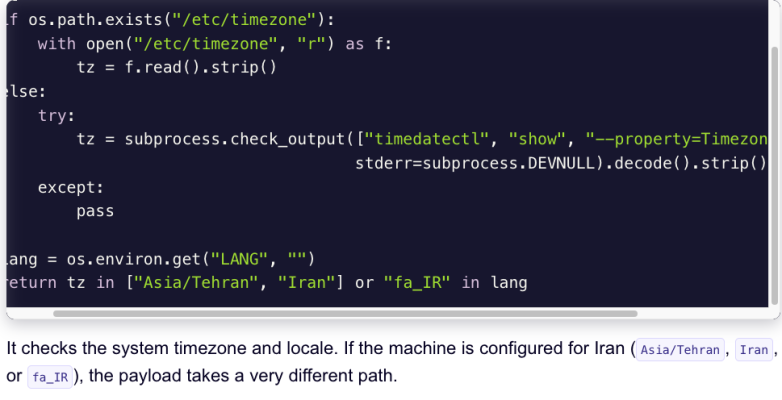
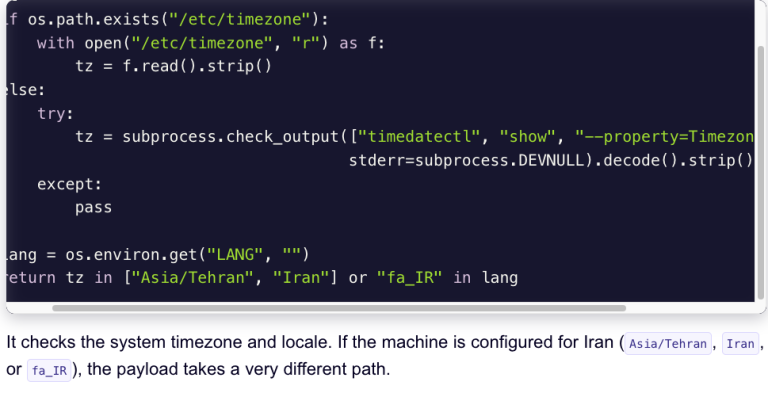
Technical analysis conducted by experts from Aikido.dev reveals that CanisterWorm operates with surgical precision. Instead of destroying everything it encounters, the worm first verifies the system's location. If the time zone does not match the parameters set for Iran, the software may limit itself to data theft. However, if the system meets the geographic criteria, a wipe procedure is triggered, which irretrievably deletes files, paralyzing the operations of institutions and enterprises.
Evolution of TeamPCP and the extortion model
The history of TeamPCP's activity dates back to December 2025, when the group began systematically attacking corporate cloud environments. Initially, their modus operandi was predictable: break-in, theft of sensitive information, and then blackmail. Communication with victims took place almost exclusively through encrypted messengers, making it difficult for law enforcement to track the flow of funds and the identities of the perpetrators. The shift from pure profit-seeking to wiper-type attacks is, however, a disturbing signal of changing priorities.
The introduction of a data-destroying component in the campaign against Iran could have several motivations. On one hand, it could be an attempt to gain notoriety in the cybercriminal underground by engaging in a high-profile geopolitical conflict. On the other hand, destroying data after it has been stolen drastically increases the pressure on the victim – the company loses not only trade secrets but also operational continuity, which could theoretically prompt faster ransom payments. However, in the case of CanisterWorm, destruction seems to be an end in itself for systems identified as Iranian.
- Self-replication: The worm automatically scans the network for further targets, eliminating the need for manual attack control.
- Precise targeting: Use of time zone and Farsi language as triggers for the wiper attack.
- Multi-vector approach: Attacking Docker, Kubernetes, and Redis servers in a single campaign.
- Extortion: Using Telegram for direct contact with victims and demanding ransoms.
Container infrastructure as the new front
What sets CanisterWorm apart from other threats is its focus on modern technology stacks. Traditional viruses often targeted vulnerabilities in Windows systems or email services. TeamPCP, however, understands that today’s highest-value data resides in the cloud, often hidden inside containers. The lack of proper network segmentation within Kubernetes clusters means that once a container is infected, the worm can quickly take over the entire production environment.
The use of the React2Shell vulnerability also suggests that attackers are closely monitoring newly discovered flaws in popular web frameworks. Integrating such exploits with a worm mechanism allows for the lightning-fast infection of thousands of servers before administrators can deploy appropriate patches. In a global context, this campaign is a warning to all organizations using Docker APIs without additional layers of authentication and monitoring. Although the current attack is targeted at Iran, the "geofencing" mechanism in the code can be easily changed to target any other region or language group.
The aggressive behavior of TeamPCP shows that cybercriminal groups are no longer afraid to enter territories previously reserved for state-sponsored APT (Advanced Persistent Threat) groups. The use of destructive code for financial or ideological purposes is becoming a new standard. Organizations must stop viewing cloud security as an option and start treating it as a critical element of survival, especially in the face of threats that can independently decide to destroy an entire infrastructure in a fraction of a second.
More from Security

$285 Million Drift Hack Traced to Six-Month DPRK Social Engineering Operation

36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants

Fortinet Patches Actively Exploited CVE-2026-35616 in FortiClient EMS

China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing
Related Articles

How LiteLLM Turned Developer Machines Into Credential Vaults for Attackers
Apr 6
Qilin and Warlock Ransomware Use Vulnerable Drivers to Disable 300+ EDR Tools
Apr 6
BKA Identifies REvil Leaders Behind 130 German Ransomware Attacks
Apr 6

