Cyberattack on a Car Breathalyzer Firm Leaves Drivers Stuck

Foto: Wired AI
Thousands of drivers lost the ability to start their cars after Intoxalock, a leader in the ignition interlock device market, fell victim to a ransomware attack. The incident, which began in mid-November, paralyzed the company's IT systems, preventing the transmission of unlock codes necessary for daily vehicle operation. Modern IID devices require regular synchronization with the manufacturer's servers to verify sobriety and update authorizations. When Intoxalock's infrastructure ceased to function, users were trapped in a vicious cycle: their devices displayed error messages or required servicing that the company was unable to authorize. The situation was exacerbated by the paralysis of the customer service hotline, leaving clients without technical support at a critical moment. This case vividly demonstrates how deeply our physical security and mobility depend on cloud stability. For IoT technology users, this incident serves as a warning sign—cyberattacks on critical service providers can have direct physical consequences, cutting us off from essential transportation tools. The vulnerability of digital infrastructure to hacking attacks thus becomes a real threat to traffic flow and personal freedom in a digitized world.
Imagine you're in a hurry to get to work, you get into your car, blow into the breathalyzer, and the system – instead of starting the engine – displays a server connection error. You are not under the influence of alcohol, but your car has just become an expensive garden sculpture because hackers launched a ransomware attack on the software provider. This is not a scenario from the series "Black Mirror," but a reality that affected thousands of drivers using Ignition Interlock Devices (IID) systems.
The attack on a company specializing in car breathalyzer technology is a glaring example of how deeply digital threats penetrate our physical mobility. In a world where road safety depends on the cloud, a single incident in IT infrastructure can paralyze transport on a massive scale. This incident coincides with disturbing reports about the activities of the FBI, which admits to the mass purchase of location data from phones, and about Iranian hacking groups targeting critical infrastructure in the medical sector.
A digital key that no longer fits
Ignition Interlock systems are installed in the vehicles of individuals convicted of driving under the influence. The device requires a breath sample before the engine starts and at regular intervals while driving. Modern units transmit data in real-time to central servers for verification and reporting to supervisory authorities. When the servers fell victim to a cyberattack, the security mechanism switched to "fail-safe" mode, which in this case meant a total lockout of the vehicles.
Read also
The problem is that the architecture of these solutions rarely anticipates a scenario of long-term lack of connectivity with the database. For users, this means not only the inability to commute to work but also the risk of violating parole conditions. From a technological perspective, we are dealing with a critical design flaw: a single point of failure. If public safety and personal freedom depend on a single data center, the entire legal-technical structure becomes extremely fragile.
- Cloud dependency: IoT devices in cars require constant online authorization.
- Lack of offline mode: Systems do not have emergency protocols allowing for driving in the event of a manufacturer outage.
- Legal consequences: Technical failure generates false reports of "missed tests," which can result in criminal sanctions for drivers.
The FBI and the data market: Privacy for sale
While drivers struggle with locked ignitions, details are emerging regarding the FBI's methods of operation. The Bureau officially admitted that it bypasses the need to obtain warrants by simply purchasing Americans' location data from commercial brokers. This is a legal gray area that turns the smartphone in every pocket into a GPS transmitter available to authorities for the right price. This data, generated by weather apps, games, or fitness tools, is aggregated and sold as a marketing product, but its precision allows for the reconstruction of every step a citizen takes.
This phenomenon sheds new light on the concept of digital surveillance. Traditional methods of surveillance require democratic and procedural oversight. Buying data on the open market is a "hacking" approach by the government toward the law, which effectively makes the Fourth Amendment to the US Constitution (protecting against unreasonable search) a dead letter. For the global tech industry, this is a signal that user data is a commodity not only for advertisers but also for intelligence agencies, forcing developers to use more restrictive data minimization methods.
Geopolitics in code: The Iranian strike on medicine
Another front in the digital war is the healthcare sector. Iranian hacking groups, likely operating under state auspices, disrupted the work of hospitals in Maryland using advanced infiltration techniques. Unlike typical profit-oriented ransomware groups, these attacks are destabilizing in nature. Blocking access to patient databases or medication dispensing systems is a direct threat to life that goes beyond the scope of ordinary cybercrime.
Analysis of these attacks points to the exploitation of known vulnerabilities in VPN systems and a lack of proper network segmentation in medical facilities. Hackers take advantage of the fact that hospitals prioritize service availability over digital security. This is a painful lesson for IT administrators: in the era of hybrid conflicts, every server with medical documentation is a potential military target. Critical infrastructure must be isolated from the public internet using more rigorous Zero Trust Architecture solutions.
"Cybersecurity is no longer an add-on to a product, but the foundation of physical safety. When the code fails, cars stop, and hospitals stop treating."
Architecture of resilience instead of blind trust
The described incidents share a common denominator: excessive trust in centralized digital systems. The technology industry must move away from a model where every end device is completely incapacitated without contact with the "mother" in the cloud. In the case of systems such as car breathalyzers, it is necessary to introduce local cryptographic keys and edge computing mechanisms that will allow the device to function even during a total blackout of the manufacturer's infrastructure.
My prediction is clear: we are facing a wave of regulations forcing IoT (Internet of Things) manufacturers to provide a so-called "right to operate offline." We cannot allow attacks on third-party companies to determine whether a citizen can go to the hospital or whether a doctor can check a patient's medical history. The future of creative and utility technology must be based on decentralization. Only by dispersing authorization points and increasing the autonomy of end devices can we avoid global paralysis when the next hacking group presses the "encrypt all" button.
More from Industry
Broadcom agrees to expanded chip deals with Google, Anthropic
OpenAI asks California, Delaware to investigate Musk's 'anti-competitive behavior' ahead of April trial
Hope for a U.S.-Iran deal, Apple's anniversary, OpenAI's podcast deal and more in Morning Squawk
AI data center boom ‘stress tests’ insurers as private capital floods in
Related Articles

The Ridiculously Nerdy Intel Bet That Could Rake in Billions
Apr 6
Researchers didn’t want to glamorize cybercrims. So they roasted them
Apr 5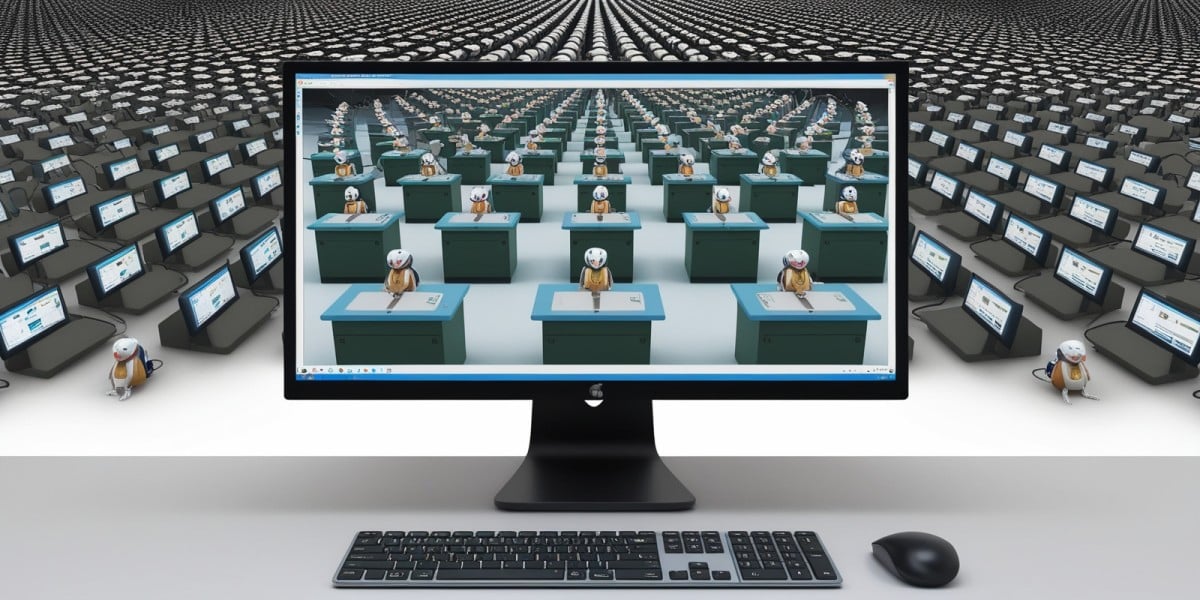
AI agents promise to 'run the business,' but who is liable if things go wrong?
Apr 5

