Scammers have virtual smartphones on speed dial for fraud

Foto: The Register
$8.3 billion – this is the estimated loss from Authorized Push Payment (APP) fraud in 2024, and Deloitte forecasts indicate that this amount will rise to nearly $15 billion by 2028. Virtual smartphones operating in the cloud, which imitate physical devices with near-perfect precision, have become a key tool in the hands of cybercriminals. According to a Group-IB report from March 2026, Cloud Phone platforms allow fraudsters to bypass advanced bank security systems by generating unique Device IDs, IP addresses, and fake sensor and GPS location data. Unlike easily detectable emulators or costly physical phone farms, virtual Mobile Infrastructure environments provide full anonymity and credibility. Criminals purchase ready-made, "warmed-up" accounts with pre-installed banking applications on forums for prices ranging from $50 to $200. For the average user, this means a drastic increase in risk; traditional anti-fraud systems often do not react to suspicious transfers because, from the bank's perspective, the transaction appears to be made from a trusted, known device. The scale of this phenomenon is forcing financial institutions to globally redefine the way digital identity is verified, as hardware parameter recognition alone is no longer a guarantee of security.
The modern smartphone has ceased to be merely a communication tool, becoming the foundation of our digital identity. It is the basis for payment systems, banking applications, and two-factor authentication mechanisms. However, this evolution has created a new, extremely dangerous front for cybercriminals. According to the latest report from Group-IB, financial fraudsters are increasingly abandoning physical devices in favor of virtual smartphones in the cloud, which imitate the behavior of real handsets with almost perfect precision, bypassing bank security systems.
The problem is urgent because traditional fraud detection methods rely on verifying the technical parameters of the device, such as a unique ID or location. Virtual phones, operating in Virtual Mobile Infrastructure (VMI) environments, can effectively deceive these mechanisms by generating fake telemetry data and even simulating readings from motion sensors, making them indistinguishable from physical hardware held in hand to banking systems.
The evolution of fraud: from SIM farms to the power of the cloud
For years, cybercriminals used physical "smartphone farms" – hundreds of cheap devices connected to chargers, managed centrally. However, this was an expensive solution, difficult to maintain, and generated enormous energy consumption. An alternative was SIM card farms using emulators, but these, in turn, were easy to detect. Emulating ARM architecture on non-ARM hardware rarely provides the credible data characteristic of a real smartphone, which quickly raised red flags in anti-fraud systems.
Read also
The ideal solution for the criminal world turned out to be Cloud Phones. These are virtual instances of the Android system running in the cloud, offering everything a fraudster needs:
- A unique Device ID for each instance.
- A dedicated IP address and spoofed GPS geolocation.
- Spoofed sensor data – simulation of an accelerometer or gyroscope, suggesting the phone is in motion.
- No need for physical service or hardware updates.
The mechanism of APP fraud and the role of "mules" in the cloud
The primary goal of using virtual smartphones is currently Authorized Push Payment (APP) fraud. This is a specific type of fraud where the victim is manipulated into voluntarily transferring funds to an account controlled by the criminal. The scale of the problem is massive – according to Deloitte forecasts from October last year, losses from APP fraud in the United States alone could rise from $8.3 billion in 2024 to $14.9 billion in 2028.
In this scheme, virtual phones serve as ideal "money mules." Criminals install banking apps on them, log into compromised or newly created accounts, and perform transfers of stolen funds. Because the virtual phone provides the same hardware fingerprint and the same behavioral patterns as a legally registered device, banking systems do not generate any warnings about suspicious activity.
"To a bank's fraud detection system, it will look like the same device that has always accessed the account – the same hardware fingerprint, the same telemetry, the same behavioral patterns," explain experts from Group-IB.
Trading in ready-made solutions is flourishing on cybercriminal forums. One can buy virtual phones there with financial apps and login data already installed, which have been previously "pre-warmed" with several small, legitimate-looking transactions. The price for such a prepared, attack-ready tool ranges from $50 to $200 per unit.
The end of the era of static security
The traditional approach of the financial sector, based on static authentication and device ID verification, is becoming insufficient in the face of cloud technologies. However, Group-IB points to certain weak points of virtual smartphones that could become the key to their detection. Virtual instances often have specific management applications installed, while simultaneously lacking the default programs that hardware manufacturers typically pre-install.
There are also behavioral anomalies that are difficult to fully fake. For example, cloud devices show a state of continuous battery charging and a total lack of sensor movement during long usage sessions. For banks that have treated these signals as secondary until now, it is time to revise their strategy. It is necessary to move toward multi-layered intelligence that combines:
- Correlation of the device environment with network infrastructure.
- Advanced user behavioral modeling.
- Graph-based analytics to detect connections between accounts.
Smartphone virtualization is further proof that technology intended to serve efficiency and savings has been rapidly adapted by the criminal world. If financial institutions do not move beyond simple device identity checks, losses from APP fraud will grow exponentially, and the "cloud phone" will become standard equipment for every digital burglar. The future of financial security no longer lies in what we know about the device, but in how deeply we can analyze the context of every operation in real-time.
More from Industry
Broadcom agrees to expanded chip deals with Google, Anthropic
OpenAI asks California, Delaware to investigate Musk's 'anti-competitive behavior' ahead of April trial
Hope for a U.S.-Iran deal, Apple's anniversary, OpenAI's podcast deal and more in Morning Squawk
AI data center boom ‘stress tests’ insurers as private capital floods in
Related Articles

The Ridiculously Nerdy Intel Bet That Could Rake in Billions
Apr 6
Researchers didn’t want to glamorize cybercrims. So they roasted them
Apr 5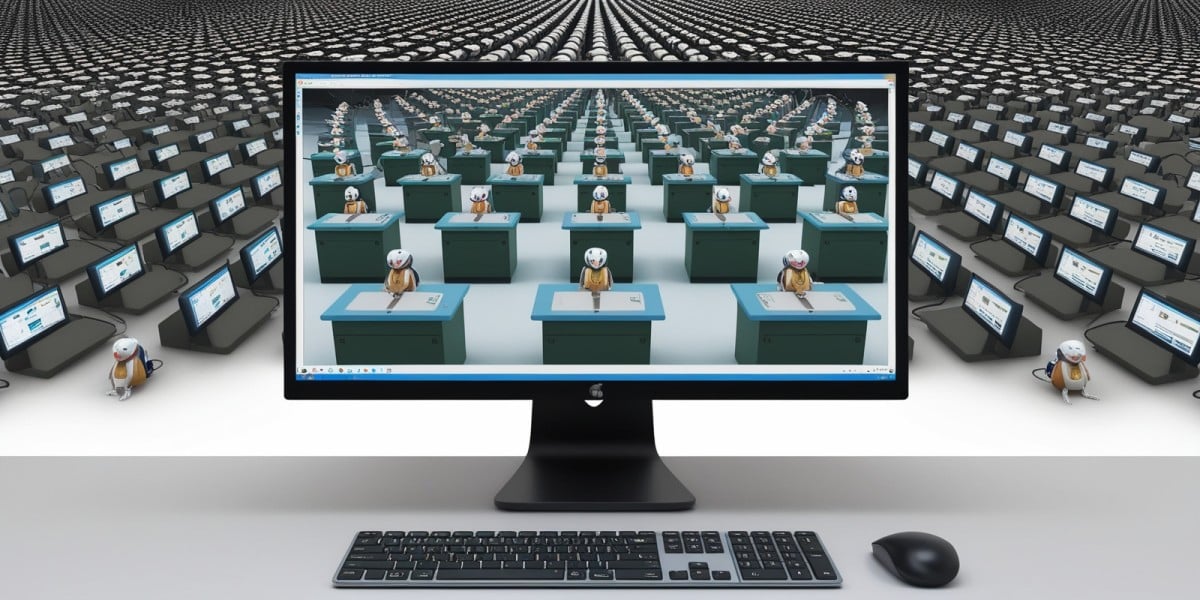
AI agents promise to 'run the business,' but who is liable if things go wrong?
Apr 5

