News — Pixelift
Latest Stories
94 articles
StartupsMar 30• TechCrunch Startups
What we’re looking for in Startup Battlefield 2026 and how to put your best application forward

SecurityMar 30
OpenAI Patches ChatGPT Data Exfiltration Flaw and Codex GitHub Token Vulnerability

IndustryMar 29
AI will write code, but prepare to babysit it - and be sure you speak its language

IndustryMar 29
The first thing vibe coding builds is confidence it will help you succeed
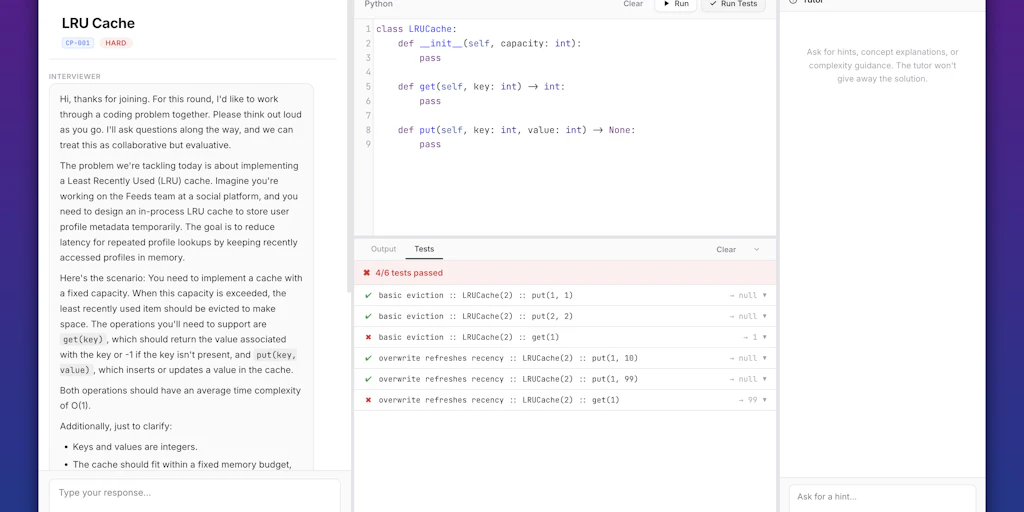
TechMar 28
CodingPrep

TechMar 28• Ars Technica
Explanation for why we don't see two-foot-long dragonflies anymore fails
TechMar 28
Getting formal about quantum mechanics' lack of causality

SecurityMar 28
Citrix NetScaler Under Active Recon for CVE-2026-3055 (CVSS 9.3) Memory Overread Bug

TechMar 27
Stop falling for scams when Norton's antivirus software is 70% off right now

SecurityMar 27
Apple Sends Lock Screen Alerts to Outdated iPhones Over Active Web-Based Exploits

SecurityMar 27• The Hacker News
TeamPCP Pushes Malicious Telnyx Versions to PyPI, Hides Stealer in WAV Files

TechMar 26
Apple discontinues the Mac Pro

SecurityMar 26
Claude Extension Flaw Enabled Zero-Click XSS Prompt Injection via Any Website

AIMar 25
The AI skills gap is here, says AI company, and power users are pulling ahead
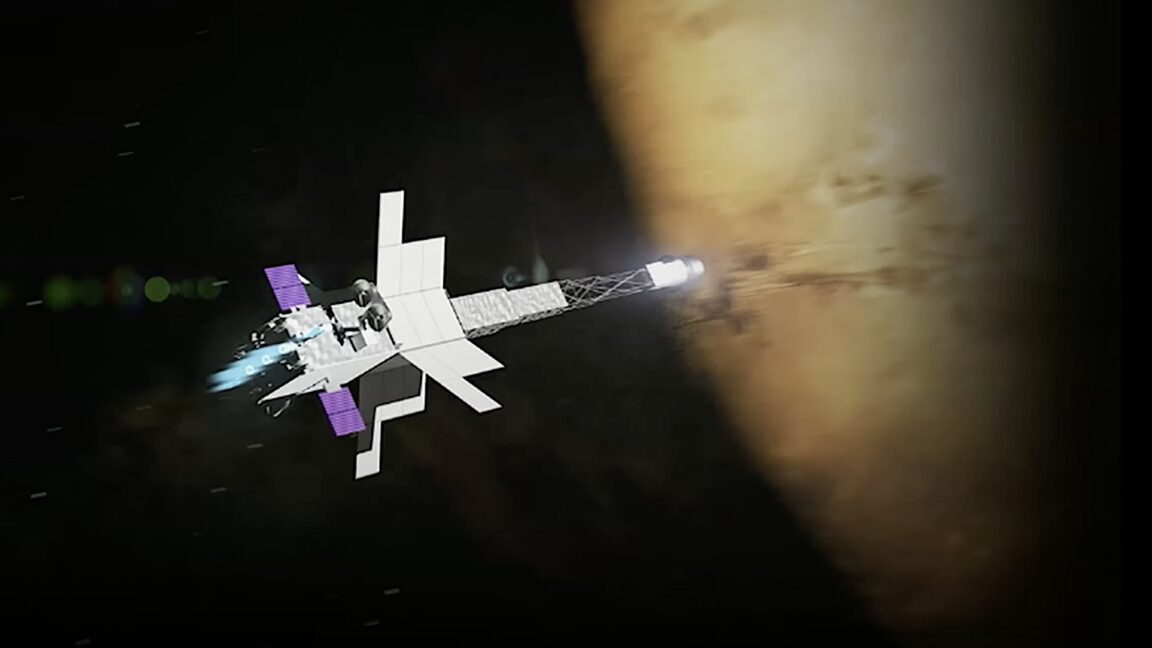
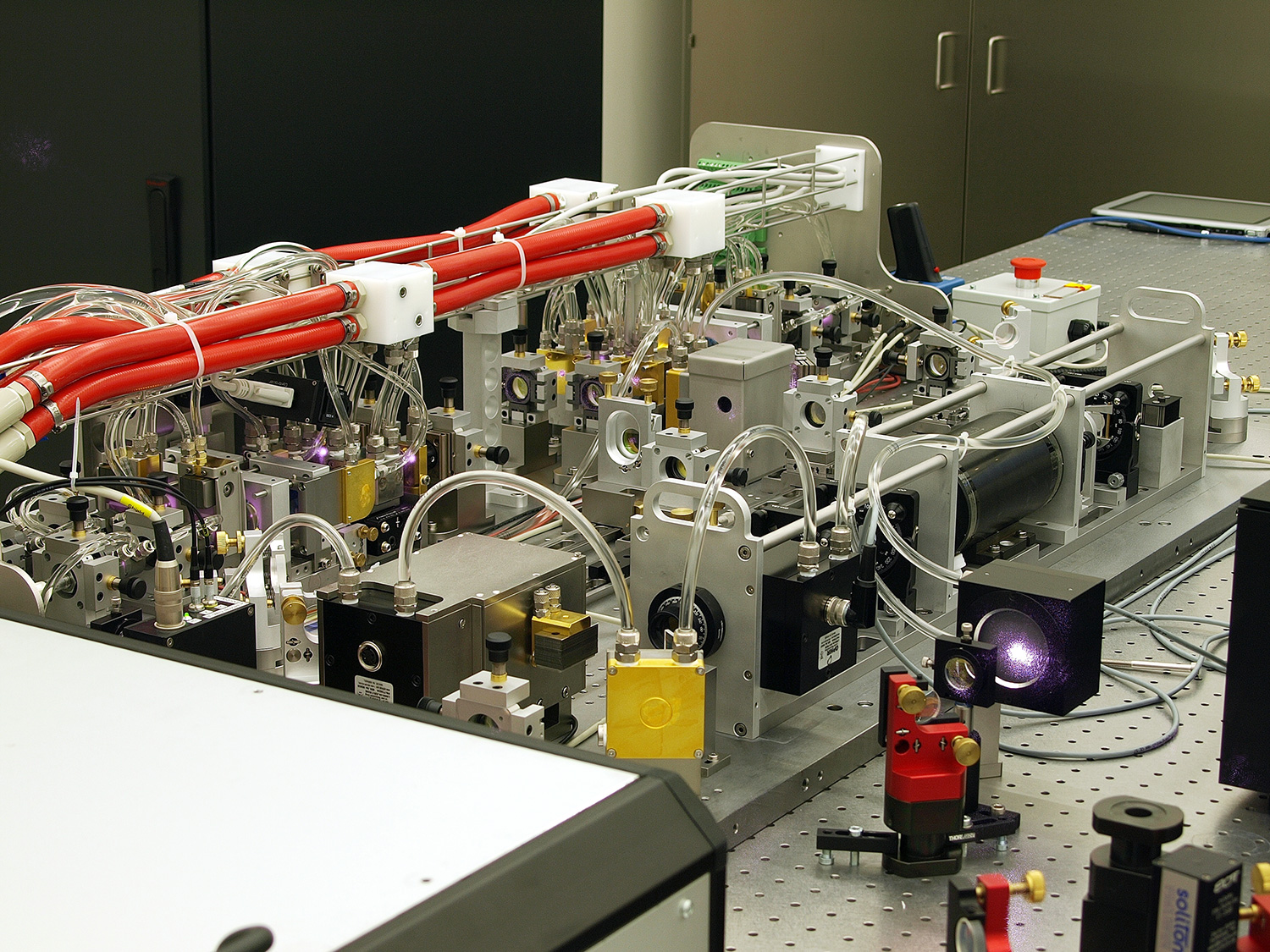
TechMar 25
Here is NASA's plan for nuking Gateway and sending it to Mars

ResearchMar 25• BBC Tech
Apple brings in age checks for UK iPhone users
ResearchMar 25
Lyria 3 Pro: Create longer tracks in more Google products

ResearchMar 25
This startup wants to change how mathematicians do math

IndustryMar 24
AI-pilled Arm CEO teases mystery products that will turn it into a money machine

ResearchMar 24
Social media bans and digital curfews to be trialled on UK teenagers

StartupsMar 24• TechCrunch Startups
Databricks bought two startups to underpin its new AI security product

AIMar 24
ChatGPT and Gemini are fighting to be the AI bot that sells you stuff

IndustryMar 24
Arm Is Now Making Its Own Chips

ResearchMar 24